Use Cases
Radiator is known for its flexibility and our products server hundreds of customers in small company internal authentication deployments to large scale ISP deployments with millions of subscribers.
This page lists various use cases of active customer deployments. To see the full description of the use case, please navigate to the dedicated use case page from the button at the end of the use case description. If your use case is not listed, please do not hesitate to contact us as there are plenty more ways Radiator can help your AAA needs.
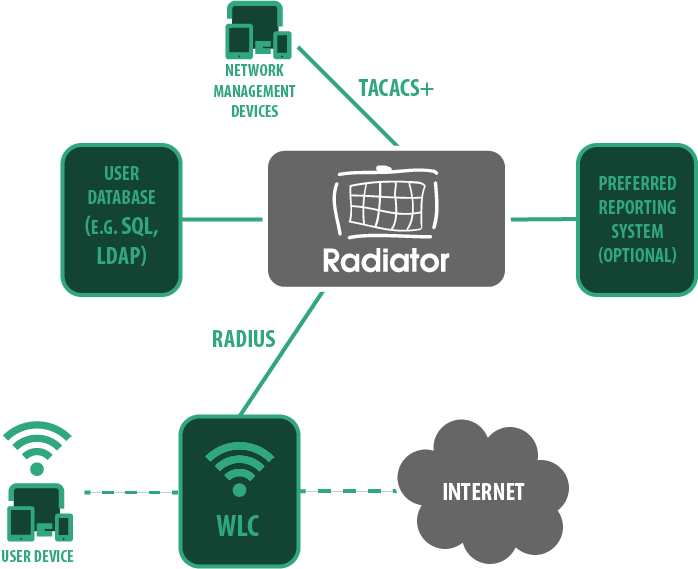
Device administration (TACACS+)
A classic use case for an AAA server is to manage administrative access to network devices such as controllers, switches and network gateways. Device administration for various types of NAS can be done with RADIUS or TACACS+ protocols.
With Radiator, you can get rid of insecure shared passwords and implement role-based access with personal user accounts. For easy user management, Radiator integrates external LDAP and SQL backends for fetching the user information and privileges. User authentication can also be combined with various MFA options for further security.
The choice between RADIUS and TACACS+ depends on security requirements in your organisation and the protocols supported by your device vendor(s). TACACS+ adds more encryption and allows more granular control for authorising each command separately, but not all devices support it. Radiator can be configured to process both RADIUS and TACACS+ requests, so you can choose one or both.
With Radiator, you can avoid vendor lock-in and freely choose the network equipment you want: Radiator includes vendor-specific attributes from over 150 vendors and adding proprietary ones or own custom attributes is made easy. This makes Radiator a great choice for multi-vendor environments.

Employee network authentication
One of the basic use cases for RADIUS authentication is employee LAN authentication, meaning employee’s authentication to both company’s internal network and the world wide web. There are multiple methods to achieve secure network connection for your employees.
At its simplest, the employee logs in with username-password combination. The network access server sends request to Radiator which checks credentials against an SQL database. Matching credentials grant access, request with wrong credentials are rejected. This solution requires local IT admin to provision WiFi credentials. This above diagram showcases some of the many pieces Radiator can integrate with in this use case, for example Active Directory or an SQL database.
When using AD the user credentials are checked against AD credentials. This model does not require manual configuration of first connection. The solution can also be complimented with second authentication factor with TOTP. All this can be implemented with just Radiator and your database of choice.
Entra ID authentication
There are numerous articles online about RADIUS authentication with Entra users, but they all mention Microsoft NPS as a mandatory intermediary piece, or as the entire RADIUS server solution – this is not the case.
Radiator Policy Server, our latest enterprise product, supports Entra ID authentication and authorisation out of the box, utilizing Microsoft Graph API for the authentication flow. This allows users to authenticate to Wi-Fi utilising their Entra credentials.
With Radiator Policy Server, you can also directly connect the Wi-Fi authentication to Microsoft Authenticator’s 2FA pop-up, something that other solutions require Microsoft NPS plugins for.


Entra ID authorisation
Some companies may prefer not to utilise the Entra credentials for Wi-Fi authentication, but would still want to use the Entra groups for authorisation decisions such as VLAN allocation. With Radiator Policy Server, it is possible to use certificate-based authentication (EAP-TLS) for authentication and do a group check from Entra for the authorisation decision.
This method allows companies to utilise pre-provisioned Wi-Fi profiles for the deployment and removes the need for credentials, while also allowing the usage of existing Entra groups. While this illustration does not show the 2FA pop-up, it is also possible to add it into this system if preferred.
Fixed-line authentication
FTTH (Fibre to the Home) services – using different PON (Passive optical network) technologies, such as GPON, XG-PON1, XGS-PON. Based on different estimates for consumer services in the industry, high-performance fibre access is needed more than ever. Because of this, one the most common new use cases for Radiator AAA server software, and especially to our Radiator Service Provider Pack is the flexible and high-powered AAA for FTTH operators.
At the core of FTTH deployments is subscriber authentication. This is where Radiator AAA server comes in. The Radiator AAA server is an industry-leading solution renowned for its flexibility, scalability, and extensive support for various authentication methods. It can authenticate users based on multiple factors, including username/password combinations, certificates, and more advanced mechanisms like two-factor authentication.


Hotel Wi-Fi (Opera PMS integration)
One of the widely seen use cases for Radiator is interoperating with different hotel property management systems (PMS). Radiator is used between the hotel’s PMS and the network equipment that controls internet access in hotel rooms. One of the commonly used systems is Micros Opera that is used by both independent hotels and hotel chains.
For Opera, we have implemented support in Radiator that is easy to deploy with your own team or with the help of our experts. When Radiator starts up, it will receive hotel customer information from Opera. This information is used for Wifi network authentication. The basic information received from Opera is name, room and customer id of the guest. When the hotel guests check in or check out, the information Radiator maintains is updated by Opera. Radiator support is not limited to Opera: it supports any PMS that provides a FIAS interface.
IoT Authentication
In today’s day and age, every machine around us is ‘smart’. Ranging from smart homes and wearables to more complex machines like cars, planes and industrial machinery, devices are connected with each other and with the internet to enhance user experience, control machines remotely and use other benefits of connectivity. This network of connected devices that communicate with each other and share information over the internet is often called Internet of Things, IoT for short.
Every one of these devices should be authenticated with secure methods when connecting to the internet, else a perpetuator can falsify data, steal information or gain access to networks through unsecure devices and networks. Companies can manage this and take control of their network by deploying a private access point name network, private APN for short.


In-Flight Connectivity
Authentication to onboard WiFi is a key component of in-flight connectivity offered by airline carriers. With Radiator, airlines can authenticate onboard Wi-Fi users to the airplane’s wireless network that is connected by other means (such as satellite connection) to the internet.
In this scenario, Radiator provides the necessary interfaces for WiFi roaming when subscribers of mobile operators are using their phones during the flight. With smooth WiFi roaming provided by Radiator AAA Server Software, end user devices can connect automatically to the in-flight WiFi network, and continue their use based on the roaming policy agreements between mobile operators and in-flight network operators.
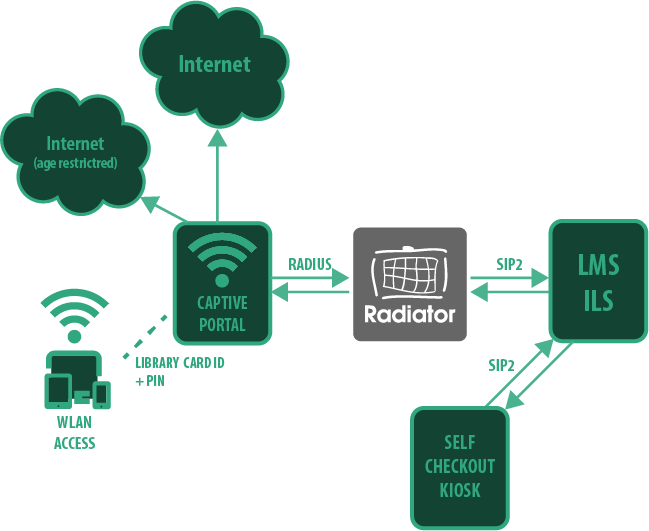
Library Systems (SIP2)
Radiator AAA server is known for its flexibility when it comes to unique use cases. This flexibility comes from the variety of supported protocols, authentication backends and logging destinations that are available in Radiator AAA server as an off-the-shelf product. Libraries are no exception to this, as Radiator supports SIP2 integration to library management systems (LMS for short, also known as integrated learning system, ILS).
Radiator can utilise existing library management systems to authenticate library Wi-Fi access for customers (often known as patrons). In its essence, Radiator will utilise patrons’ existing library card credentials for the authentications. Typically these credentials are used to loan and return books on self-checkout lending machines. This method has many benefits. First, it gives library patrons easy access to the internet without handing a common public password. Second, the internet access can be modified or disallowed based on patron status or information, for example age restrictions can be applied.

Multi-factor Authentication
Adding multi-factor authentication to your network is a proven solution to improving network security. Radiator supports a great deal of TOTP and HOTP based authenticators, both as applications and as physical tokens.
Cloud based MFA solutions have limitations in situations where internet connectivity is unreliable, or external connections are limited due to security reasons. Radiator can be deployed on-premise and generate TOTP seeds for authenticator apps, resulting in a fully offline, standalone AAA with easy to use MFA. Physical tokens from Yubikey and RSA can also be used with offline deployments.
Policy and Charging
When operators want to add quotas or pre-paid plans for their subscribers with Wi-Fi offloading or VoWiFi functionality enabled, translation between RADIUS-based Wi-Fi network components and Diameter-based billing systems are usually needed.
Radiator Policy and Charing Pack support a variety of Diameter interfaces for integrations between RADIUS-based Wi-Fi and fixed-line network components and Diameter-based mobile network components. We’ve compiled the use case descriptions onto the Radiator Policy and Charging Pack product page.
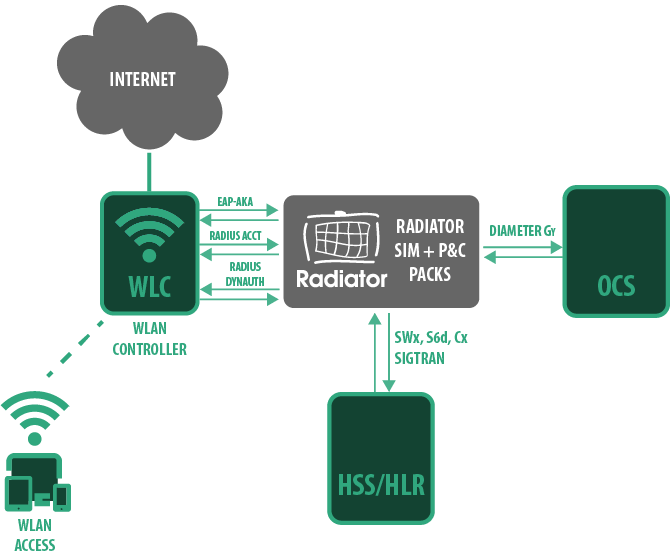

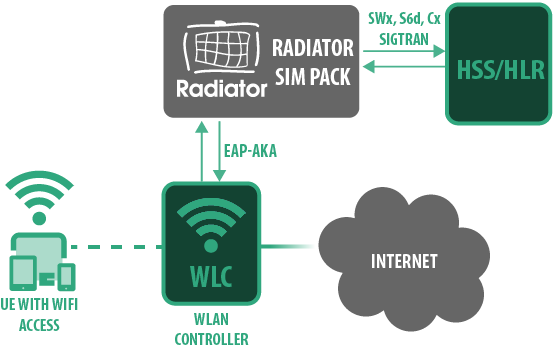
Voice over Wi-Fi (VoWiFi)
In recent years there has been a significant rise in Voice over Wi-Fi (VoWiFi) in different markets. With VoWiFi, carriers and operators are increasing their indoor coverage overnight to provide better voice coverage to their subscribers and making at the same time savings in their traffic costs. With automatic SIM authentication, enhanced with IMSI Privacy, end-users will never have to consider whether they are connected to a mobile network or to their domestic WiFi network, for example.
Doing seamless call transfer support between WiFi and mobile networks new opportunities for operators. With VoWiFi voice calls and messaging work seamlessly for the end-user – and the operator retains control of the traffic.
Wi-Fi Offloading
In busy locations with high volumes of mobile traffic like sports stadiums, shopping malls, public transport hubs and underground metros, SIM- and eSIM-based devices can automatically switch from mobile data connections to local Wi-Fi networks.
Transferring the data traffic to Wi-Fi networks reduces the load on the mobile network, which improves the coverage and the user experience. In addition, using Wi-Fi roaming services, such as Google Orion Wi-Fi or OpenRoaming, can further reduce costs when carriers can use these additional services for Wi-Fi offloading.

Wi-Fi Roaming eduroam
eduroam (short for education roaming) worldwide wireless network for educational and research institutions worldwide. It allows students, researchers, and staff from eduroam connected organisations to connect to the internet at any eduroam-enabled location using their home institution’s login credentials. These credentials are often username and password issued by the home organisation.
Radiator can and has been used for all levels of eduroam. Radiator Software’s experts have contributed to development for over two decades. Radiator AAA is used by over 100 universities across the world.
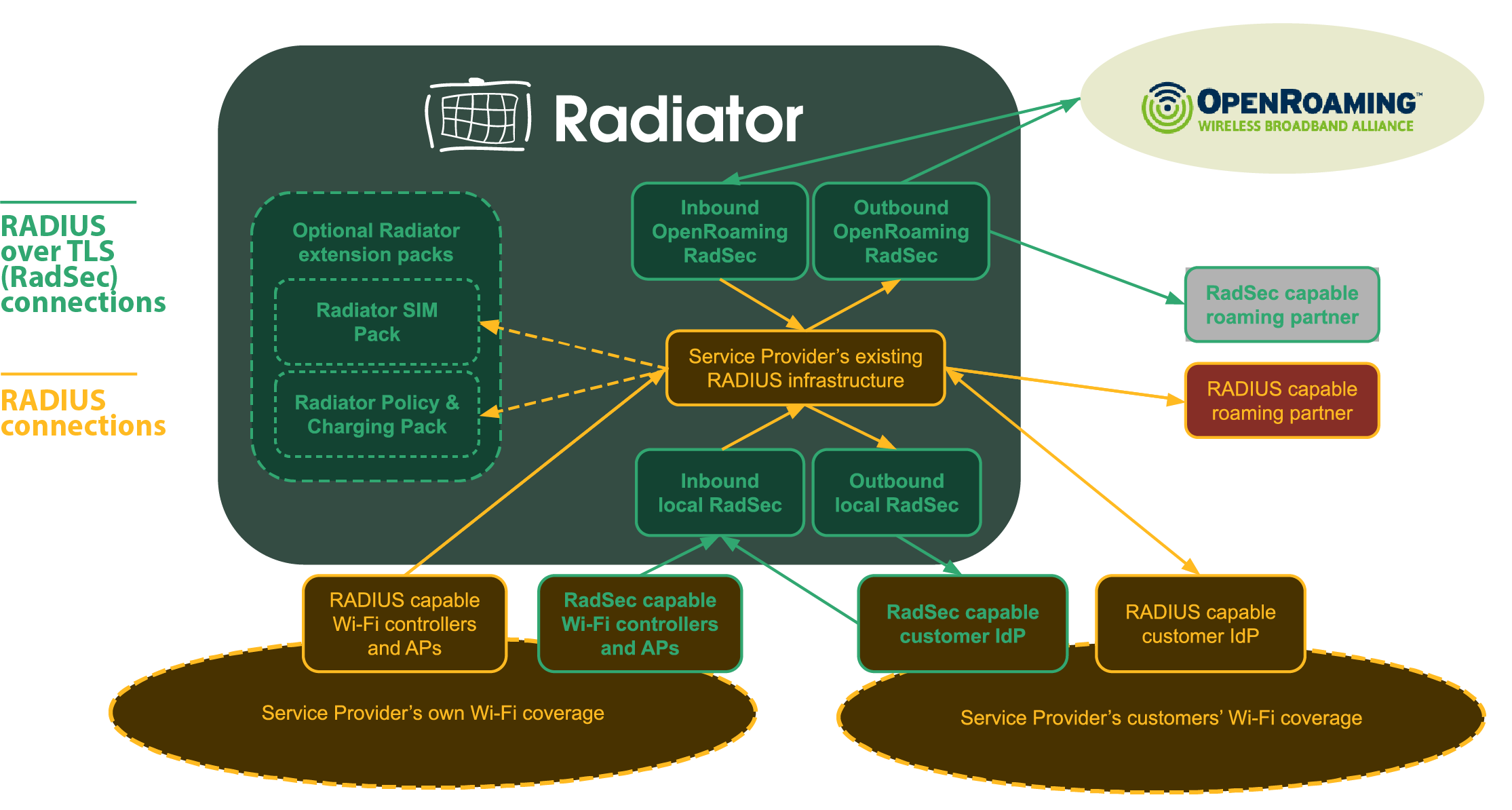
Wi-Fi Roaming OpenRoaming
OpenRoaming is a technology and commercial ecosystem for WiFi connectivity. End users with credentials from any participating organisation can seamlessly login to secure Wi-Fi in all OpenRoaming locations.
OpenRoaming federation members include access network providers (ANPs) who provide the wireless connectivity, and identity providers (IdPs), who provide user credentials to end users, with many organisations acting in both capacities. Radiator provides solutions for both ANPs and IdPs.